Homepage Slideshow
AgenticAI-Driven TPRM: Risks & Opportunities
Watch Now On-Demand!
https://executiveitforums.org/10841-a-proactive-framework-for-the-digital-age
Demonstrating the Value of Cybersecurity
Watch Now On-Demand!
Coordinating TPRM Efforts
Watch Now On-Demand!
Incorporating Al into Your GRC Program
Watch Now On-Demand!
Best Practices to Combat Ransomware
Watch Now!
Enriching Third-Party Risk Processes with Targeted Risk Intelligence
Watch Now On-Demand!
Latest News
- GhostPoster Campaign Exploits Firefox Add-Ons to Spread Malware
- SoundCloud Breach Exposes Millions of User Emails Amid Follow-Up Attacks
- CISA Releases Updated Cybersecurity Performance Goals to Strengthen Critical Infrastructure
- Researchers Warn of Four Sophisticated Phishing Kits Targeting Global Users
- Banks Face Urgent Call to Upgrade IT Systems for Customer Vulnerability Standards
- Microsoft Ends 2025 with 56 Security Fixes, Including Actively Exploited Flaw
- CommBank launches national AI and cybersecurity programme for SMEs
- U.S. Warns of Brickstorm Backdoor Malware Targeting U.S. Infrastructure
- The WebXR Leak: A Hidden Browser Flaw Exposed Millions to Risk
- WordPress Sites Under Attack
- EU Reaches Deal on New Payment Services Regulation to Bolster Fraud Prevention
- New Android MaaS Threats Expand On-Device Fraud and Remote Control Capabilities
- OpenAI Confirms Mixpanel Breach: Limited API User Data Exposed, ChatGPT Unaffected
- Legacy Python Packages Expose Risk of PyPI Supply Chain Attacks
- Nationwide Cyberattack Disrupts CodeRED Emergency Alert System
- Microsoft Teams Guest Access Leaves Organizations Exposed to Security Bypass Attacks
- Global financial community completes switch to ISO 20022
- Cyber Intrusion at SitusAMC Triggers Data Exposure Fears for Major US Banks
- Global Malvertising Campaign Exploits Trusted Software Installers
- Ex-Revolut Founders Secure $10M for AI Compliance Startup Condukt
On-Demand
-
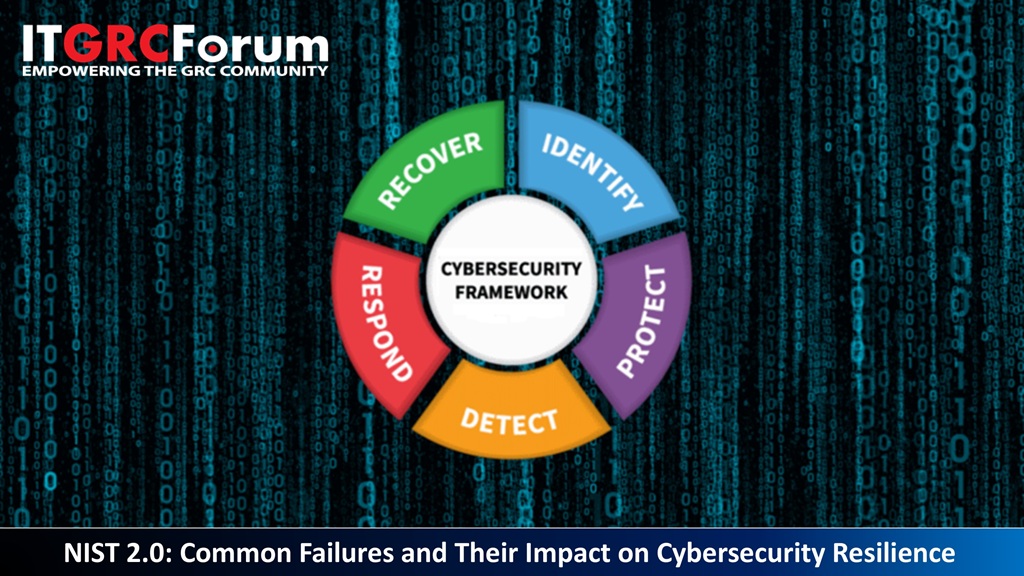 NIST 2.0: Common Failures and Their Impact on Cybersecurity Resilience
NIST 2.0: Common Failures and Their Impact on Cybersecurity ResilienceRecorded: December 17 | 2025 Watch
This CPE webinar will explore real-world challenges in implementing the NIST Cybersecurity Framework 2.0 (CSF 2.0), examining their consequences and providing actionable strategies to strengthen cybersecurity resilience. Our panel will unpack the complexities of NIST 2.0, highlighting common pitfalls—from misaligned risk assessments and inadequate governance to weak supply chain risk management and inconsistent framework adoption.
-
 Modern TPRM: Strategies for Securely Onboarding Vendor Software
Modern TPRM: Strategies for Securely Onboarding Vendor SoftwareRecorded: December 4 | 2025 Watch
From malware-laced updates to vulnerable open-source dependencies, attackers are increasingly targeting the vendor software that enterprises rely on to operate their business. According to a recent Gartner survey on Third Party Risk Management, 83% of Cyber risk professionals find risks embedded within vendor applications after deployment.
-
 Generative AI in Risk and Compliance: Insights from the 2025 Industry Report
Generative AI in Risk and Compliance: Insights from the 2025 Industry ReportRecorded: November 12 | 2025 Watch
Despite billions invested, 95% of organizations see limited returns from generative AI. Our new research shows why: without elite risk management, firms cannot deploy this technology confidently or take the strategic risks that unlock true business value.
-
 Generative AI Security: Preventing AI from Becoming a Data Breach Multiplier
Generative AI Security: Preventing AI from Becoming a Data Breach MultiplierRecorded: November 5 | 2025 Watch
Generative AI tools are revolutionizing enterprise productivity, but they also introduce a new set of risks that IT GRC leaders must address head-on. Misclassified data, over-permissioned access, and uncontrolled sharing can cause AI systems to surface sensitive information to the wrong people. Without the right guardrails, the benefits of AI can quickly be overshadowed by data exposure, compliance violations, and governance gaps.
-
 AgenticAI-Driven TPRM: Innovation, Risks, and Opportunities
AgenticAI-Driven TPRM: Innovation, Risks, and OpportunitiesRecorded: October 22 | 2025 Watch
As third-party risk management (TPRM) becomes more complex, AgenticAI is emerging as a powerful force reshaping how organizations identify, assess, and manage vendor risks. This session will examine the innovations AgenticAI brings to TPRM, the risks and challenges it introduces, and the opportunities it creates for building stronger, more resilient programs.
-
 Managing Active Directory Like It’s 2003 Leaves You Exposed in 2025
Managing Active Directory Like It’s 2003 Leaves You Exposed in 2025Recorded: October 15th | 2025 Attend
Active Directory (AD), Windows Server, and the threat landscape have all evolved. Has your approach kept pace?
-
 The Million Dollar Blindspot - Business Privileged Access Management for Non-Routine Transactions
The Million Dollar Blindspot - Business Privileged Access Management for Non-Routine TransactionsRecorded: September 25th | 2025 Watch
The Business Agility Paradox
In today's volatile business environment, organizations face an inherent tension between operational agility and regulatory compliance. Standard business processes are governed by established controls, approval workflows, and business policies. -
 Coordinating TPRM Efforts: A Multi-Departmental Approach
Coordinating TPRM Efforts: A Multi-Departmental ApproachRecorded: August 14th | 2025 Watch
As third-party risk management (TPRM) programs mature, successful organizations are increasingly taking a cross-functional approach—aligning stakeholders from procurement, IT, legal, compliance, and risk to build a unified strategy. This CPE-accredited webinar brings together subject matter experts from ProcessUnity and OneTrust to explore best practices for breaking down departmental silos and fostering collaborative governance.
-
 Zero Trust, Full Control: Tackling the Modern Identity Crisis in Data Security
Zero Trust, Full Control: Tackling the Modern Identity Crisis in Data SecurityRecorded: September 10th | 2025 Watch
In today’s increasingly decentralized IT environments, organizations are facing a modern identity crisis—one where traditional perimeter-based security is no longer effective, and identity has become the new attack surface. As cloud adoption, remote work, and third-party access proliferate, the risk of overprivileged users, identity sprawl, and unauthorized access to sensitive data continues to grow.
-
 How to Stop Rubber-Stamping User Access Reviews within Regulated Applications
How to Stop Rubber-Stamping User Access Reviews within Regulated ApplicationsRecorded: July 10th | 2025 Watch
Most User Access Reviews (UARs), especially in SOX-scope applications and other regulated environments like SAP, Oracle, and Workday, are performed to meet compliance requirements — not because they drive meaningful security outcomes. They’re repetitive, rubber-stamped, and void of risk context.
-
 Incorporating Al into you GRC Program for Business Agility
Incorporating Al into you GRC Program for Business AgilityRecorded: June 26th | 2025 Watch
Managing governance, risk, and compliance (GRC) in a fast-paced world can feel like chasing a moving target, and AI might just be the edge you need to keep up.
-
 Managing Vendor Risks in the Cloud: Insights for Internal Oversight
Managing Vendor Risks in the Cloud: Insights for Internal OversightRecorded: June 4th | 2025 Watch
As cloud adoption accelerates, managing vendor risks is more crucial than ever. Join our panel discussion webinar with Paul McKay, Principal Analyst at Forrester, and subject matter experts as we explore strategies for overseeing vendor relationships in the cloud. This session will provide practical guidance and exclusive research to strengthen your approach.