2013 SXSWi Security Trends in Technology
South by Southwest Interactive (SXSWi) is an incubator of cutting-edge technologies. The event, which takes place every March, features five days of compelling presentations from the brightest minds in emerging technology, scores of exciting networking events hosted by industry leaders, and an unbeatable lineup of special programs showcasing the best new websites, video games and startup ideas the community has to offer.
At the SXSWi conference this year, mobile was a big deal—which meant mobile applications and their security are high on developers’ radars.
Mobile Security
Access Point states, “Developers need to make sure they cover one other major concern when creating a mobile app: security. Consumers need to feel and know that their information is secure at all times, and developers need to lead the charge before they ask for additional measures. Creating simple but effective security checkpoints is a must—just make sure they are not so obtrusive that your users get annoyed and are resistant to adopting your application.”
Another point of interest at this year’s SXSWi was authentication. With all the data breaches over the last decade, the conversation to eliminate the username/password as a simple access point has begun. One painfully overlooked authenticator is the driver’s license. Gemalto presented a compelling program on why the simple plastic license needs a makeover.
Driver’s Licenses
Technology impacts our lives daily, but one item is not advancing—your driver’s license. A simple card made of plastic with a few bar codes, a magnetic stripe and a photo is all it is. By finding or even simply viewing one, someone can immediately access your personal information to use for fraudulent purposes. Stealing someone’s identity is way too easy. Most industries have already gone digital; now it’s time to tackle the DMV.
A new method of identification is needed: an electronic driver’s license (eDL). One simple chip (or smart card) could revolutionize decades of using the same technology—paper and plastic. EDLs stand to increase security and offer more privacy. The adoption of eDLs also lays the groundwork for a truly mobile wallet solution.
Robert Siciliano, is a personal security expert contributor to Just Ask Gemalto and author of 99 Things You Wish You Knew Before Your Mobile was Hacked!.
Unknown Credit Card Charges: Fraud or Legit?
Recently, my mother-in-law discovered that a pretty significant piece of jewelry had gone missing. There had been a number of construction workers in the house for a few weeks and when she went to get her jewelry, it was gone. After searching like a crazy person under/in/on top of everything, she called the police.
When the police arrived they asked a bunch of questions, did an onsite investigation and calmly and collectively stated to her: “You misplaced it. It probably hasn’t been stolen. You will find it in a few days.”
Visibly upset and a little teary eyed, she thanked the officer for his time and collapsed in her chair. Two days later, as she was folding laundry, there it was, nestled with her undergarments. She swears to this day she didn’t put it there, but it must have fallen into the drawer from the top of the dresser on a day she was putting laundry away.
Frankly, minus the calling the police, I’ve done the exact same thing.
When charges are made to our credit cards, it’s very easy to look at a charge, not be familiar with it and immediately suspect fraud. Each month, I reconcile my statements at least twice—first weekly when current charges are made and then when my final statement comes in. And without fail, there is at least one charge that gets me all in a tizzy and requires me to do my own investigation.
When you come across one of those questionable charges (and you will), don’t panic until you take these steps.
#1: Look up the name of the company online. Generally you will find something that will immediately trigger your memory as to what you bought and from whom.
#2: Check your receipts against the dollar amount charged and also look for the company name.
#3: Some merchants include a phone number as part of their merchant information on the receipt. Call the number and be cordial to the person on the phone.
#4: If all else fails, call your credit card company and dispute the charge. You will have to give up some basic information,but the credit card company will get to the bottom of it within two billing cycles.
#5: Sign up for BillGuard for free. BillGuard monitors your credit card charges and alerts you to any potential fraud. If there are any grey charges, BillGuard will flag them and let you know.
Robert Siciliano is a personal security expert & advisor to BillGuard and is the author of 99 Things You Wish You Knew Before Your Identity Was Stolen. See him knock’em dead in this identity theft prevention video.
College Students Need to Protect Wireless on iPads
A recent study estimated that nine out of ten undergraduate students will own a smartphone by the time this year’s crop of freshmen is slated to graduate. As this demographic grows, college students are increasingly at risk of having their privacy compromised. Mobile-using students also tend to use unprotected public WiFi networks more, which adds additional risk factors to their profile. These factors combine to transform the generation that grew up using the internet most frequently into the generation that’s the most vulnerable online.
Hotspot Shielda wireless VPN has been downloaded more than 100 million times on PCs, Macs, iOS and Android platforms. The company experienced explosive growth in 2012 and, according to Quantcast, is among the top 35 online destinations based on total internet traffic.
The new version of the popular application includes:
- Privacy protection for anonymous web communication, browsing and sharing online at dorms, cafes and offices.
- Twenty percent greater mobile data savings capabilities, saving users up to $30 per month in mobile data fees.
- The ability to access US and UK TV shows and other services online by switching IP addresses—a must-have when traveling abroad.
- A new user interface that makes it easier than ever to view bandwidth savings and manage features.
To celebrate the launch, AnchorFree will kick off a contest to help US and UK college students keep their digital lives private and secure: the Hotspot Shield College Privacy Challenge, with $50,000 in scholarship awards distributed among the top three finishing universities. During the Challenge, any college student registering with a school-provided “.edu” or, in the United Kingdom, “.ac.uk,” email address will receive a free subscription to Hotspot Shield VPN for iPhone,Android, PC and Mac for one full year—up to a $42 value. The contest begins April 1 and will run through June 9.
More information about the Hotspot Shield College Privacy Challenge can be found athttp://college.hotspotshield.com.
Robert Siciliano is an Identity Theft Expert to Hotspot Shield VPN. He is the author of 99 Things You Wish You Knew Before Your Identity Was Stolen See him discussing internet and wireless security on Good Morning America.
What You Should be Aware of When Using Your Android Device
As we all migrate towards using smartphones and tablets, we need to be aware of the risks associated with them. Most of us know that we need to protect our computers with security software, but we don’t always take that precaution with our mobile devices. In fact nearly 75% of Americans do not use mobile security software and 36% of us don’t even use a basic PIN to lock our devices.
And if you’re an Android user there are some things you want to be aware of.
Mobile malware is growing and mostly on Android – Android has become the most popular mobile platform for hackers to target, and this past quarter, McAfee Labs™ found that all new forms of malicious mobile software were aimed solely at the Android operating system (OS).
There are a number of factors why mobile malware is growing rapidly on the Android OS. One of which it is the fastest growing platform and has the largest share of the mobile marketplace, and by nature, cybercriminals go where the large numbers are.
Malicious mobile activity is growing via apps – the mobile malware growth above is mostly from bad apps. And these bad apps can do anything from access your contacts and send them emails to “see” everything you do on your mobile device including typing in your user name and passwords to your financial accounts.
Watch app permissions – Android developers can choose from over 150 different permissions that the app can access on your mobile device. Some of these include turning on your camera and recording what it sees, accessing all your contacts and even accessing your IMEI code (which is like your phone’s Social Security number)! You just need to be aware of the type of app and why it would need to access certain information so it’s not sending your personal information to hackers.
For the moment, the amount of detected smartphone malware is relatively low compared to malware that targets desktop or laptop PCs; but being aware that it exists is the first step toward protecting yourself and your data. Here are some steps you can do to protect yourself:
First and foremost, use a PIN to lock your device.
Like with your computer, be cautious when clicking on links, especially from people you don’t know. And make sure you have web protection software which will prevent you from going to malicious sites.
When downloading apps, do your research and check it out before downloading. Read the ratings and reviews and only purchase apps from well-known reputable apps stores.
When you install an app, make sure you review the permissions it’s accessing on your device. And use an app protection feature that warns you if your apps are accessing information on your mobile that it doesn’t need to.
Install a comprehensive mobile security solution like McAfee Mobile Security that includes anti-malware as well as web protection, anti-theft and app protection features. Or if you want to protect all your devices, including your mobile devices, you can use McAfee All Access that protects all your PCs, Macs, smartphones and tablets.
Robert Siciliano is an Online Security Expert to McAfee. He is the author of 99 Things You Wish You Knew Before Your Mobile was Hacked!
How NFC and Security Work Hand in Hand
NFC is an acronym for near field communication, a wireless technology that allows devices to talk to each other. In the case of a mobile wallet application, those devices would be a mobile phone and a point-of-sale device, such as a credit card reader at a checkout counter. NFC can be used in other ways beyond credit card transactions. It can integrate with hardware, such as your car, to lock or unlock a door.
Consumers perceive a lack of security with NFC, but in fact NFC is much more secure than having your data stored on a magnetically striped credit card, which can be more easily compromised. There are numerous layers of security in an NFC payment, including both hardware and software, and major payment networks such as MasterCard and Visa require certification before any payment application or hardware is let loose on the public.
There are important key features that reinforce mobile NFC security:
1) NFC SIM cards storing a consumer’s payment credentials and the payment applications are certified according to security standards. These standards are defined by financial services’ authorities and are comparable to CHIP-N-PINsecurity.
2) Consumers can choose to authenticate transactions by entering a PIN code on the payment application. Consumers can also request the PIN to be entered for all payments, even for small amounts—providing the end-user with complete control over protection features.
3) Secure over-the-air technology for remote management enables immediate remote blocking of the payment application. This works in a similar fashion to blocking a bank card in opposition mode.
Check out NFC and see if your device offers NFC here and definitely give it a try!
Robert Siciliano, is a personal security expert contributor to Just Ask Gemalto and author of 99 Things You Wish You Knew Before Your Mobile was Hacked!.
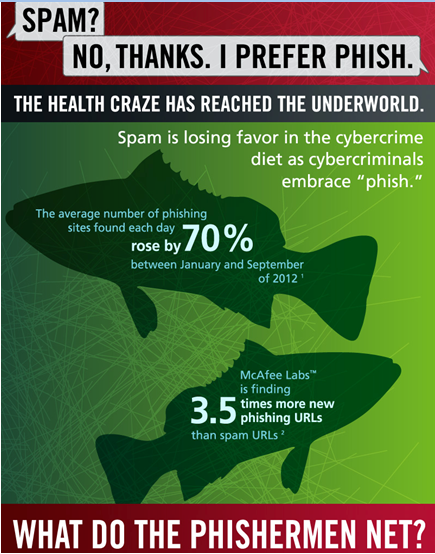
Criminals Prefer Pheasting on Phish Over Spam
Most of us are aware of spam, and while we may think it’s just an annoyance, what’s really dangerous about it is the fact that most spam are phishing attempts. Phishing is when cybercriminals attempt to fraudulently acquire your personal information, such as passwords and credit card details, by masquerading as a trustworthy person or business in electronic communications, such as email, texts or instant messages.
Criminals have long known there’s a sucker born every minute. In fact, more than 9 million households have had at least one member who gave up their information to phishers. And in the first half of 2012, these cybercriminals netted over $680 million which may be one of the reasons that McAfee Labs™ saw the average number of phishing sites found each day, increase by 70% between January and September of 2012. They also found 3-1/2 times more phishing URLs than spam URLs for the first time ever. This means spam is losing favor (and flavor) to phishing as cybercriminals are tossing out wide phish nets.
Here’s a graphic that explains how phishing works:
There are no depleted phish stocks in the sea of scamming, so to protect yourself from phishing you should:
Be suspicious of emails that ask for personal or financial information. Most banks and legitimate businesses will not send you an email asking you to provide this type of information.
If you suspect that an email or chat message may not be authentic, or you don’t recognize the sender, do not click any links included in the message.
Check your bank, credit and debit account statements regularly for any unauthorized transactions. If you notice any suspicious or unfamiliar transactions, contact your bank and/or card issuer immediately.
Make sure to keep your browser and operating system up to date and install any necessary security patches.
Use comprehensive security software, like McAfee All Access, on all your devices and make sure they include a safe search tool that identifies risky websites in email, chat, social networking sites and search engine results to protect you from phishing.
Robert Siciliano is an Online Security Expert to McAfee. He is the author of 99 Things You Wish You Knew Before Your Mobile was Hacked!
Iran Blocking VPNs on its Already Strangled Internet
Free societies really have no idea what it’s like to live in a censored and controlled nation that locks down the internet and filters what citizens are allowed to consume.
Imagine wanting to login and research information on health or find a friend online or simply watch some funny videos on YouTube…only to discover that your government doesn’t allow it.
In Iran, the UK-based group Small Media reported,“Prominent Persian-language websites and other online services have been filtered one by one, and communications with external platforms is becoming progressively more difficult.”
Iran isn’t the only country like this. Countries with some kind of internet censorship are frequently Middle East and North Africa (MENA) countries, as well as some countries in Southeast Asia and China. Specifically, Saudi Arabia, UAE, Qatar, Bahrain, Yemen and others in the MENA region block a lot of content and often communication applications like Skype, Viber and social media sites. Pakistan has blocked YouTube; in Vietnam, some ISPs block Facebook; some Central American countries block communication apps as well.
Reuters reports, “A widespread government internet filter prevents Iranians from accessing many sites on the official grounds they are offensive or criminal.”
“Many Iranians evade the filter through use of VPN software, which provides encrypted links directly to private networks based abroad, and can allow a computer to behave as if it is based in another country.”
“But authorities have now blocked ‘illegal’ VPN access, an Iranian legislator told the Mehr news agency on Sunday. Iranian web users confirmed that VPNs were blocked.”
It’s not just users in Iran who relyon US or European-based services that enable them to tunnel around the government censorship. One of the most popular, which has seen explosive growth in recent years, is Hotspot Shield VPN, in part because it offers a free, ad-supported version. Many other VPNs can be quite costly for users in developing countries where censorship is most prominent. Hotspot Shield also has a good track record of continuing to work even when other services get blocked, as was the case in Iran. So if you have friends or relatives living in or traveling to countries experiencing internet censorship, you might want to let them know about this useful service.
Robert Siciliano is an Identity Theft Expert to Hotspot Shield VPN. He is the author of 99 Things You Wish You Knew Before Your Identity Was Stolen See him discussing internet and wireless security on Good Morning America.
10 Tips for a Safe and Secure Spring Break
Spring has arrived, and students are gearing up to head to warmer climes and tear it up on spring break. Coming from a dad who a) tore it up a bit at that age himself and b) lives and breathes safety/security, I have a few tips—from low tech to high tech– to keep teens and twentysomethings from getting into trouble, becoming victimsorhaving their identity stolen, which—believe-me—will put a real damper on a vacation.
#1 Don’t be stupid. I know this is easier said than done. Anyone who plans a spring break trip which involves partying amongst thousands of other teens is actually planning on getting stupid. That’s not a successful plan. Make smart choices and be careful.
#2 Eat. You’re probably going to be consuming alcohol. Eat and eat often. Alcohol is poisonous; food absorbs the poison and can helpprevent you from getting sick or too intoxicated (in-toxic-ated).
#3 Moderation. Everything in moderation, including alcohol. Negative side effects of too much alcohol can mean bad hangovers or even death.
#4 Cover your drink. There are lots of idiots who think it’s fun and funny to drug people by slipping drugs into drinks. Get your own drink and cover it up with your hand or a napkin.
#5 Use the buddy system. Never leave a friend alone, especially if he or she is inebriated.
#6 Use a designated driver. Seriously. Or cab it.
#7 Watch out for aggressive people. It is a sad fact that too much alcohol makes men get aggressive and women sometimes become vulnerable. Beware of this and don’t become a Spring Break statistic.
#8 Protect your wallet. Cash, credit cards, IDs, etc. should go in your front pocket. Have a photocopy of everything accessible online.
#9 Locate/Lost/Wipe. Install software to locate or wipe a lost mobile device, and make sure it’s password protected.
#10 WiFi security. Whether on a mobile, tablet or laptop, you’re going to be connected to the internet at some point. And just like there are predators out there waiting for you to slip up so they can take advantage of you, there are criminal hackers looking to swipe your wireless data and access your accounts to steal your identity. Download Hotspot Shield VPN for your iOS, Android, PC and Mac to encrypt all your wireless internet traffic.
Robert Siciliano is an Identity Theft Expert to Hotspot Shield VPN. He is the author of 99 Things You Wish You Knew Before Your Identity Was Stolen See him discussing internet and wireless security on Good Morning America.